Telegram OSINT Tools 2026: 5 Tested Bots That Actually Work
Telegram is a data canyon. If you're an OSINT analyst, you know the struggle: 90% of the "leak bots" floating around are dead ends, scams, or just straight-up malware. You don't have time to waste on tools that return null results.
We tested the popular ones so you don't have to. Below are the 5 tools that still return valid data in 2026. No fluff, just the capabilities and the real talk on what works.
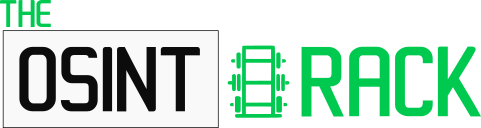
1. @TrueCalleRobot – Phone to Name Lookup (One-Way)
Straightforward phone number intelligence. You feed it a number, it returns the associated name and potential metadata. No reverse lookup, no noise.
Key Capabilities:
- Phone → Name Resolution: Retrieves the registered nominative associated with a phone number.
- Metadata Expansion: May return additional linked data (carrier, region, associated accounts) when available.
- One-Way Query Only: Does NOT support reverse lookup (name → phone). Designed for phone-first investigations.
- Fast Response: Typically returns results in seconds with minimal rate limiting on free tier.
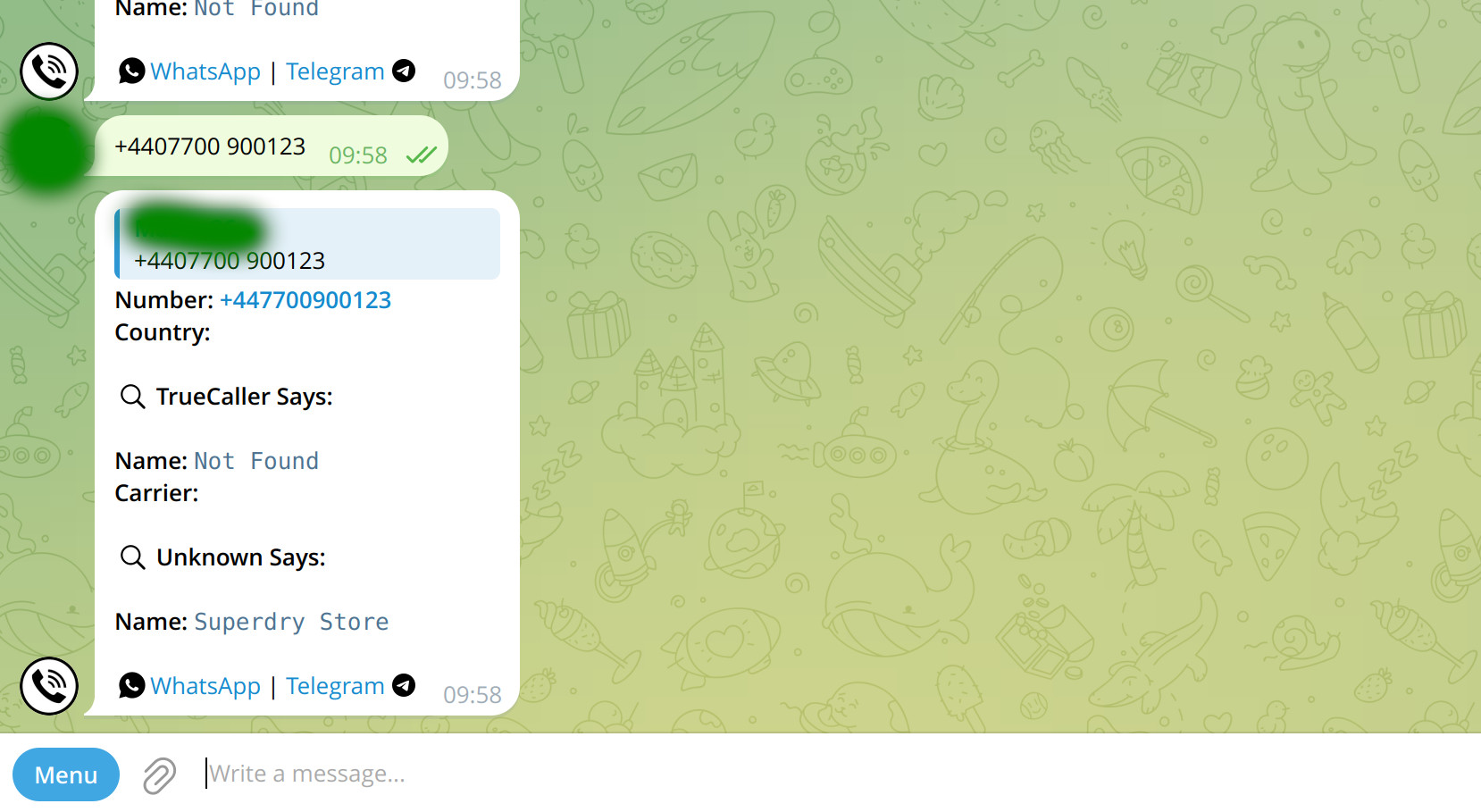
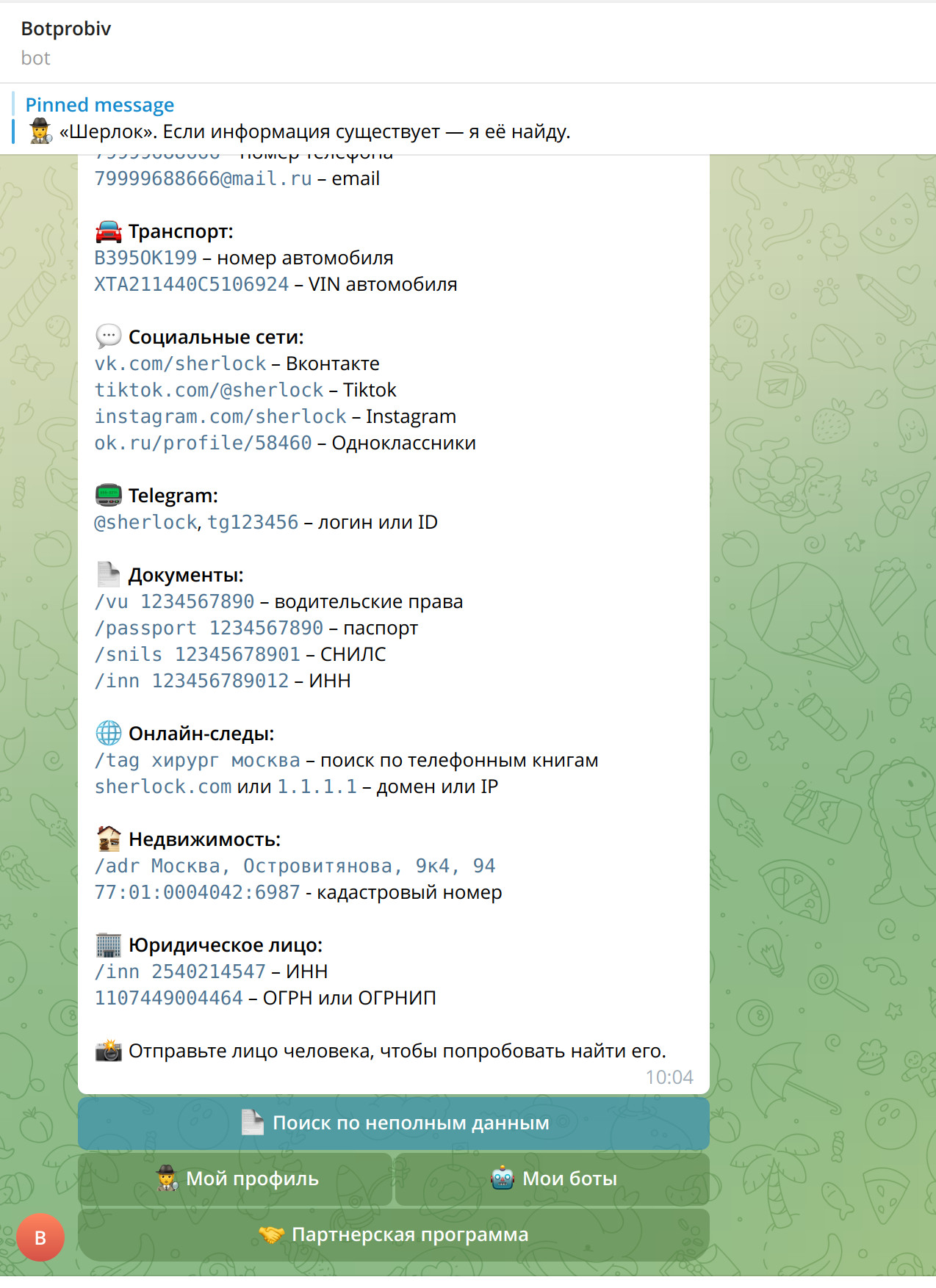
2. @probiv43bot – The Russian Platform (Crypto-Paid, Frequently Banned)
The classic Russian-style OSINT bot. Gets banned, reappears under new handle, repeat. Data source appears consistent across iterations. Crypto payments, limited free lookups.
Key Capabilities:
- User ID / Username Lookup: Retrieves account metadata, registration info, and linked identifiers.
- Phone Fragment Matching: Returns partial phone data or associated emails when available in source DBs.
- Crypto Payment Integration: Accepts crypto for premium queries; free tier offers limited daily lookups.
- Resilient Infrastructure: Frequently migrates to new bot handles; community channels often share backup invite links.
3. @fwqfgq_bot – Same Group, New Handle (Backup Links Required)
The Vibe: Same operator group as probiv43bot. Same data sources. Same crypto payment model. Gets shut down regularly—always keep the backup invite link handy because the current handle might vanish in days or weeks.
Key Capabilities:
- Phone Number Recon: Converts phone numbers to Telegram User IDs and associated metadata.
- Multi-DB Query: Checks against aggregated leak databases, not just Telegram-specific sources.
- Backup Channel System: Provides invite links to mirror channels when the main bot gets banned.
- Free Tier Limits: Offers a handful of free lookups before requiring crypto payment for bulk queries.
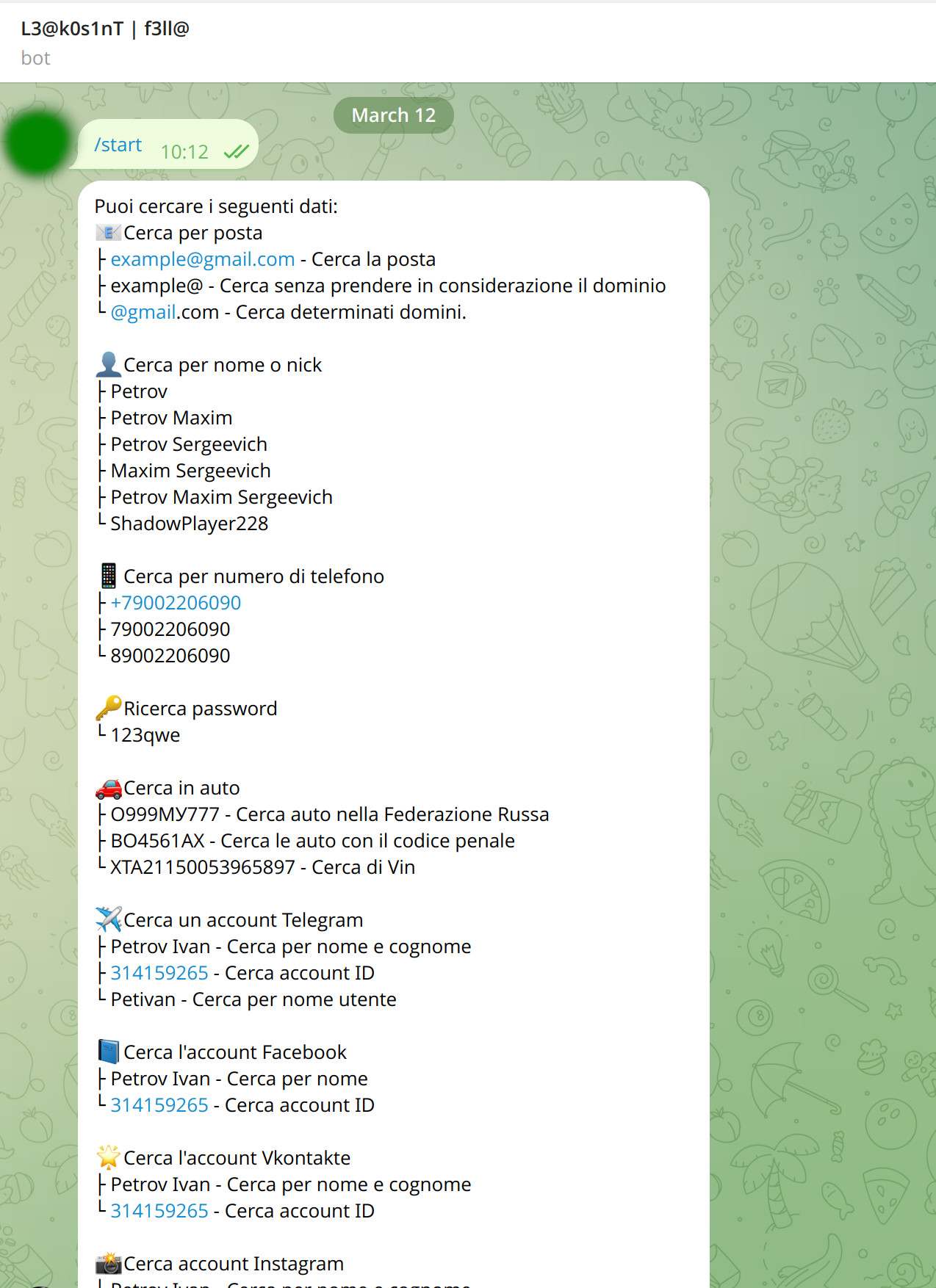
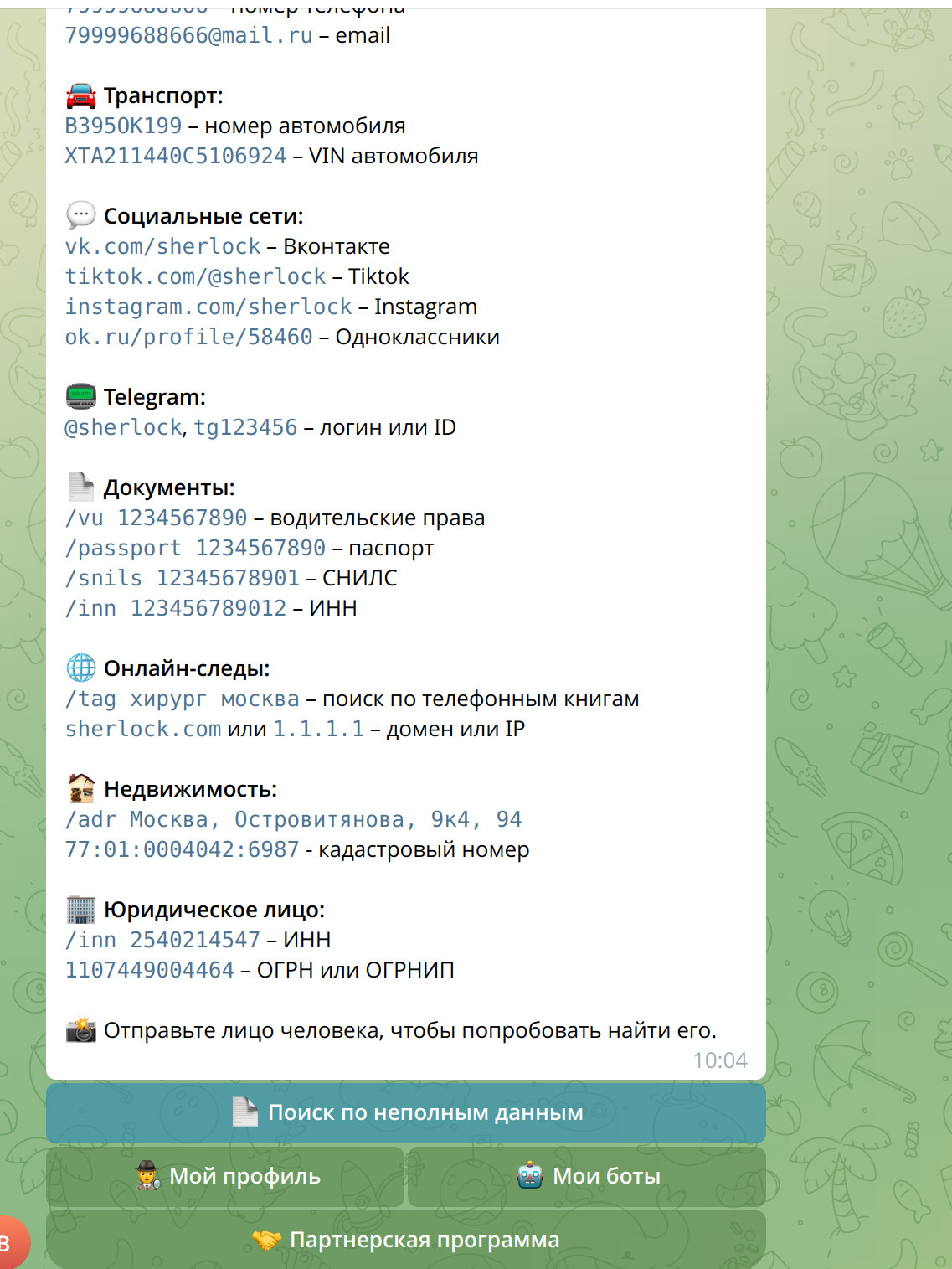
4. @LeakOsintf311a_bot – Multi-Language Leak Search (No Cyrillic Stress)
The Vibe: Similar backend to the Russian-style bots, but with a crucial UX upgrade: auto-language detection. The bot adapts to your Telegram language settings, so you're not wrestling with Cyrillic menus if you don't speak Russian.
Key Capabilities:
- Auto-Language Adaptation: Detects your Telegram language config and serves menus/results accordingly.
- Cross-Platform Leak Search: Queries Telegram, email, and social media breach databases in one call.
- Breach Source Tagging: Labels results with the source database (e.g., "Collection #5", "Telegram Dump 2024").
- Freemium Access: Free tier allows basic queries; premium unlocks bulk export and deeper historical data.
5. @rockstar_probiv_bot & @svnpgc_number_to_details_bot – Bulk Leak DB Access
Two bots, same wavelength. Slightly different UI, same massive backend: multi-gigabyte leak databases containing Telegram chat dumps, credential leaks, and aggregated breach data. If the data exists in a public(ish) leak, it's probably indexed here.
Key Capabilities:
- Massive Leak DB Queries: Access to multi-GB databases containing Telegram chat exports, credential dumps, and breach aggregates.
- Phone / Username / Email Search: Supports lookup by multiple identifier types across platforms.
- Batch Query Support: Premium tier allows bulk lookups for large-scale investigations.
- Export Formatting: Results can be exported in JSON or CSV for report integration.
How to Stay Safe While Doing OSINT
Using these tools without opsec is a rookie mistake. Here's how to keep your identity secure while investigating others.
- Use a Burner Account: Never use your main Telegram account for querying leak bots. You will get flagged, and your number could end up in a future leak. Create a fresh account with a temporary number.
- Don't Download Executables: Some "advanced tools" linked in bot menus are just malware in disguise. Stick to inline bots and web dashboards.
- Legal Boundaries: Gathering public data is OSINT. Doxing people with it is a crime. Know the difference. Don't cross the line from analyst to aggressor.
- Assume Instability: These bots operate in a gray zone. Today's working handle might be banned tomorrow. Always have backup links or alternative tools ready.
FAQ (People Also Ask)
Q: Are Telegram OSINT bots legal?
A: Using them for research is generally legal. Using them for doxxing, stalking, or harassment is illegal in most jurisdictions. Always check your local laws regarding data privacy.
Q: Can I find someone's exact location with these bots?
A: No. Unless they shared their live location publicly (which is rare), these tools only provide digital footprints (IP logs, linked emails, past breaches), not real-time GPS coordinates.
Q: Why do some bots ask for payment?
A: Maintaining databases of leaks costs money. Free bots usually have rate limits or outdated data. Paid tiers offer real-time access and deeper historical records.
Q: Why do these bots keep getting banned?
A: Many operate in a legal gray area by indexing leaked data. Telegram periodically shuts them down for ToS violations. Operators often re-launch under new handles-hence the need for backup channels.
Stay sharp, stay anonymous, and keep your data clean.